The cyber threat landscape is evolving rapidly, and businesses of all kinds are working hard to keep up with the pace of change. Unfortunately, keeping up with the pace of digital threats may not be enough, and businesses may be leaving themselves exposed in their frantic attempts to maintain security and reliability.
The gold standard for business is to remain ahead of the curve. This way, organizations are not simply struggling to keep their heads above water but are instead proactively identifying and mitigating threats even before they arise. But how is this done?
Security providers such as IBM advocate an integrated and comprehensive approach to cybersecurity. This is a unified strategy in which data can flow easily between cybersecurity solutions, ensuring complete insight into cybersecurity profiles and statuses in real time. It is also a seamless approach, with no weak spots or areas of vulnerability. All endpoints are protected to the same high degree.
The Security Immune System
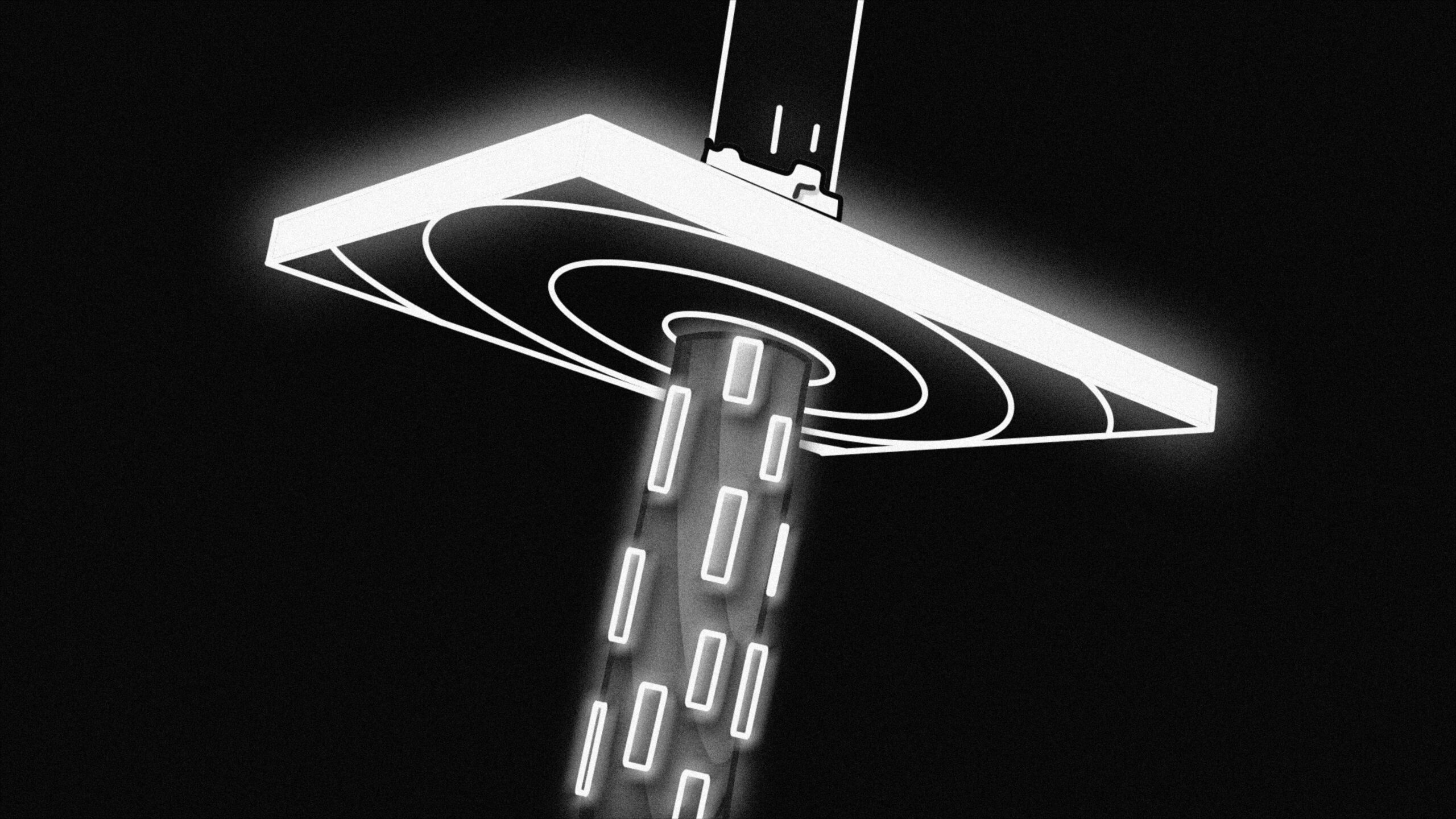
A unified and comprehensive cyber threat protection solution mirrors the processes and protocols we see in action in the natural world. In fact, we only need to look within ourselves to witness this kind of natural system in action. Our internal immune system is a harmonious set of processes that proactively maintain health and well-being for the rest of the body.
Infections are detected, and warning signs are learned. Then the body works to mitigate these infections, retaining the crucial data required to fight pathogens and illnesses in the future. Different parts of the body work together to spot the signs of infection and to achieve a harmonious and proactive defence.
IBM has taken inspiration from this, developing the IBM Security Immune system as a way to implement a cultural shift in the way we approach cybersecurity. With more than 1,200 product vendors in a crowded market, it is easy for business owners to find themselves working with a granular and distributed setup, with a lack of communication and collaboration between different solutions.
The Security Immune System combats this, bringing together data processing and analysis, security apps, mobile strategies, threat intelligence, identity and access, and a number of other components of your security initiatives. All of these components are linked via a centralized security orchestration and analytics hub, achieving a holistic and comprehensive security strategy.
Integrated Strategies Rising to the Challenge of Cybersecurity
Cybersecurity is among the greatest challenges facing modern businesses, as threat profiles evolve and grow at a frightening pace. Business owners have identified the following areas as their greatest challenges in today’s landscape:
- 45% of business owners said that reducing average incident response and resolution time was their primary challenge.
- 41% described ongoing improvement of security analytics as their greatest challenge.
- 40% cited keeping on top of emerging threats and vulnerabilities.
- 31% cited filling a shortage of skilled cybersecurity staff.
- Additionally, 52% of business owners said they expected improving their security threat analytics to be the main challenge in the coming two to three years.
Despite these challenges, the situation has improved — 80% of business owners report that incident response speeds have accelerated significantly in the last two years, improving by 16% on average. Much of this improvement has come from an increasingly unified and integrated approach to cybersecurity, although the statistics tell us there is still some distance left to travel before businesses are able to meet security challenges in an effective and proactive manner.
The key is to approach cybersecurity holistically. By recognizing that all aspects of cybersecurity are linked — and that no individual aspect can afford to stand alone, isolated from the rest — businesses can begin to achieve the conceptual shift required to modernize their security strategy.
It is this kind of shift that IBM is seeking to nurture with its Security Immune System approach.
The Risks of Non-Integration in Cybersecurity
The danger of granularity and isolation of key components within your cybersecurity setup is severe. While most businesses are already experiencing challenges within their strategies, a disparate set of security elements will not only fail to meet these challenges but can also actively increase vulnerability.
- Data siloing that hinders response
Data is always a vital element when it comes to handling cybersecurity challenges, providing the insight and understanding required to combat threats. However, if there is no integration between different components of your strategy, data runs into bottlenecks and obstacles. When data siloing occurs — and insight cannot flow freely between different system components — it is very difficult to mount a meaningful response to threats.
- Isolated components that are not fit for purpose
The idea of a solution with robust components existing in isolation is an outdated one. In the modern threat landscape, there is no such thing as a one-size-fits-all quick fix. Instead, components need to be highly specialized — designed to rise to specific challenges with high levels of efficiency and efficacy. In other words, an effective component does not exist in isolation, and channels of communication and collaboration between different security components are critical to overall success.
- Points of weakness and vulnerability
Perhaps the key problem with a non-integrated system is coverage. You wouldn’t place waterproof sheets side by side and expect this to keep out the rain — instead, you would apply waterproof sheeting in an overlapping fashion, sealing any seams and joints to prevent leakage. The same is true with your cybersecurity solution — overlaps and reinforcement are required to eliminate vulnerabilities across all endpoints.
Unify Your Cybersecurity Strategy with IBM
IBM is seeking to position itself among the leaders in the cybersecurity defence and strategy field, helping business owners to achieve a more proactive, positive, and predictive approach to security with end-to-end solutions. We are an IBM Platinum partner, which means we are licensed to provide the firm’s full suite of products and solutions to enterprise customers. With these solutions on your side, an integrated cybersecurity strategy is within reach.
Our product offerings include IBM Cloud for Security, IBM QRadar, and IBM Security SOAR, among others. Reach out today to learn more, or browse the product specs on our site.